Table of Contents
Introduction
In previous articles, such as Network Packet Broker Powered by SONiC: PB-APP Solution, we introduced Asterfusion’s packet broker platform. It supports full-rate interfaces from 1G to 800G.
This article discusses best practices for inline packet broker deployment to maximize network security.

What is Packet Broker ?
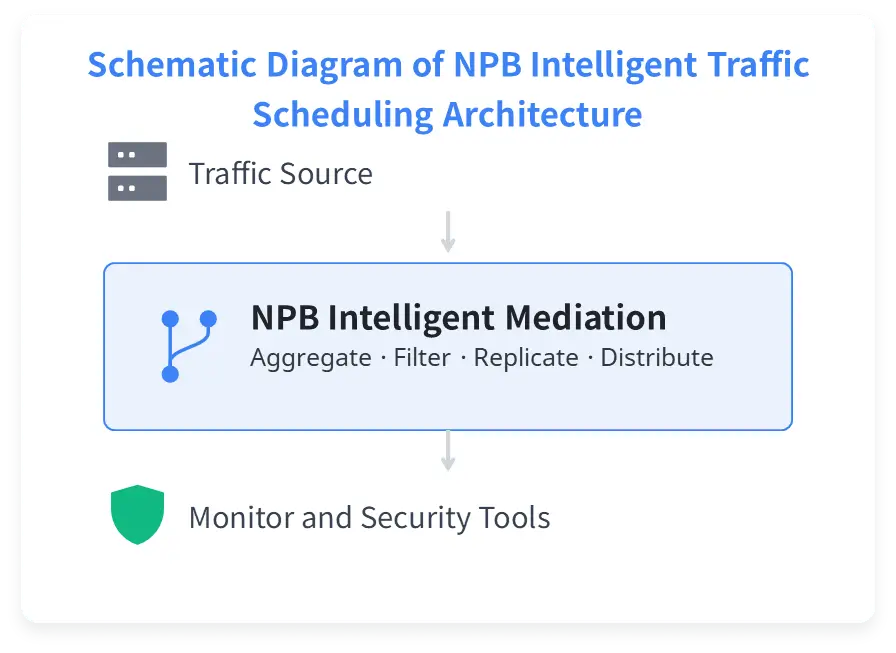
First, let’s review the definition of a packet broker. A packet broker, also called an NPB (Network Packet Broker), acts as an intelligent intermediary. It performs traffic filtering, replication, and aggregation. It then distributes the required traffic to backend tools with precision, improving tool utilization.
A key characteristic of Asterfusion’s new-generation packet broker is that it runs as containerized software on a switch, based on the SONiC operating system. Unlike traditional standalone NPB appliances, it integrates switch functionality with NPB capabilities.
Why Do We Need Inline Packet Broker Deployment?
Traditional passive deployment has clear limitations. It can only monitor traffic passively and cannot perform complex traffic filtering.
In an inline deployment, the NPB sits between the source and destination. It can actively process traffic, such as dropping or modifying packets. This differs from the traditional out-of-band model, which only allows passive analysis.
The need for inline deployment is mainly reflected in the following aspects:
- Address the limitations of out-of-band monitoring In out-of-band mode, the NPB cannot affect the original traffic. If abnormal packets must be blocked or modified, inline deployment is required.
- Improve backend tool efficiency Through traffic filtering, replication, and aggregation, only the required traffic is delivered to backend tools. This avoids unnecessary resource consumption.
- Enable active attack mitigation Once attack signatures are detected, packets can be dropped or blocked immediately.
Key Technologies in Inline Packet Broker Deployment
In an inline packet broker deployment, several key technologies are used to achieve fine-grained traffic management.
- ACL Rules
Unlike traditional switch ACLs that are mainly used to block traffic, ACLs on a packet broker are used for traffic selection.
Traffic can be filtered based on fields such as VLAN, IP address, and port number. The selected traffic is then marked and forwarded. This enables a complete workflow of traffic selection, tagging, and distribution.
- VLAN Tagging
In this scenario, VLAN is not used for broadcast domain segmentation. It is used as a traffic label.
The VLAN tag identifies the source port of the traffic. For example, traffic from port A can be tagged with VLAN 101. Backend tools can identify the VLAN tag and return the processed traffic to the correct link. The VLAN tag is removed before the traffic re-enters the production network to avoid service impact.
- Load Balancing
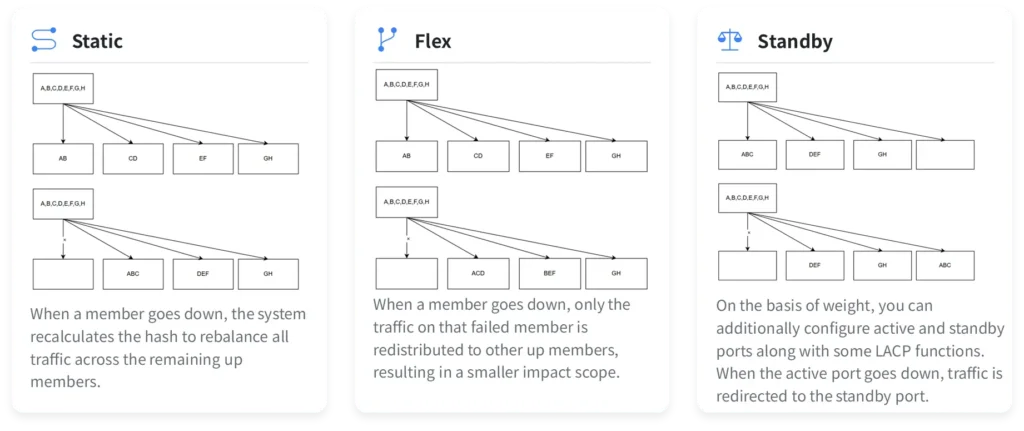
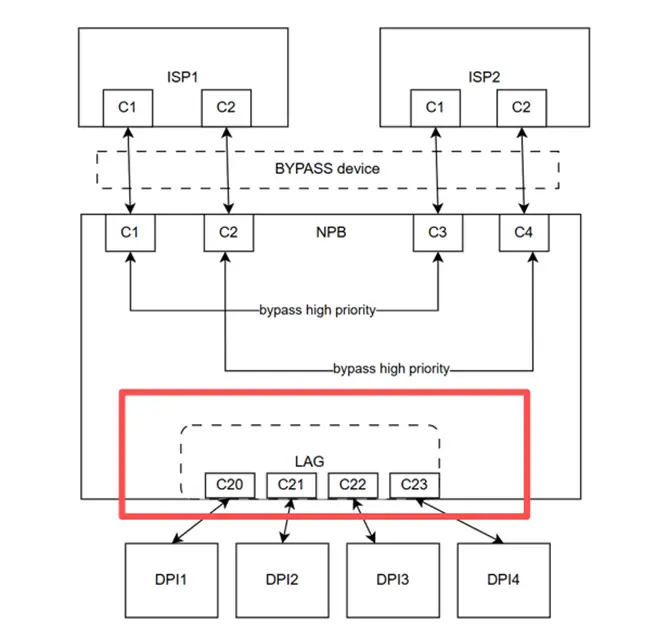
Three load balancing modes are supported: static, resilient, and active/standby. These modes ensure traffic continuity if a backend tool port fails.
The resilient mode is recommended. It redistributes only the traffic from the failed device. Traffic on other devices remains unchanged. This minimizes the impact on running tools.
- High Availability Design
High availability is a key requirement for inline packet broker deployment.
In addition to link aggregation (LAG) redundancy, the following mechanisms improve reliability:
- Built-in bypass forwarding templates: when a LAG interface goes down, a predefined template is activated automatically to keep traffic forwarding.
- High-priority traffic bypass: routing protocol frames, such as EtherType 0x8809 and 0x88CC, are forwarded directly. They bypass DPI or other inspection devices. This ensures reliable delivery of controlled traffic.
The NPB forwarding pipeline is simple and efficient. It is different from traditional switches that rely on MAC learning and routing protocols.
Packet forwarding is entirely rule-based. The administrator only defines the ingress port, ACL processing policy, and egress port. Traffic can then be forwarded precisely.
This protocol-independent model provides high flexibility. It is well suited for complex traffic steering scenarios and significantly improves traffic management efficiency and response time.
Typical Network Topology and Configuration
Network Architecture:
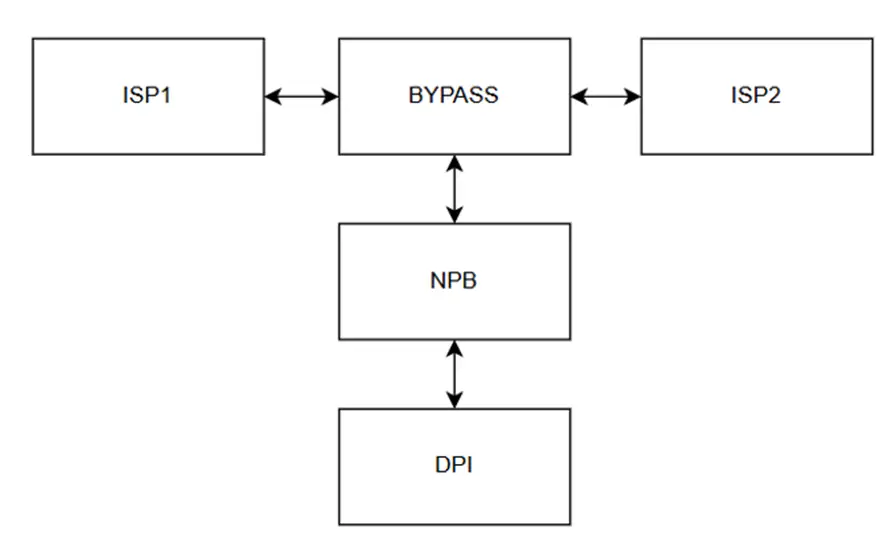
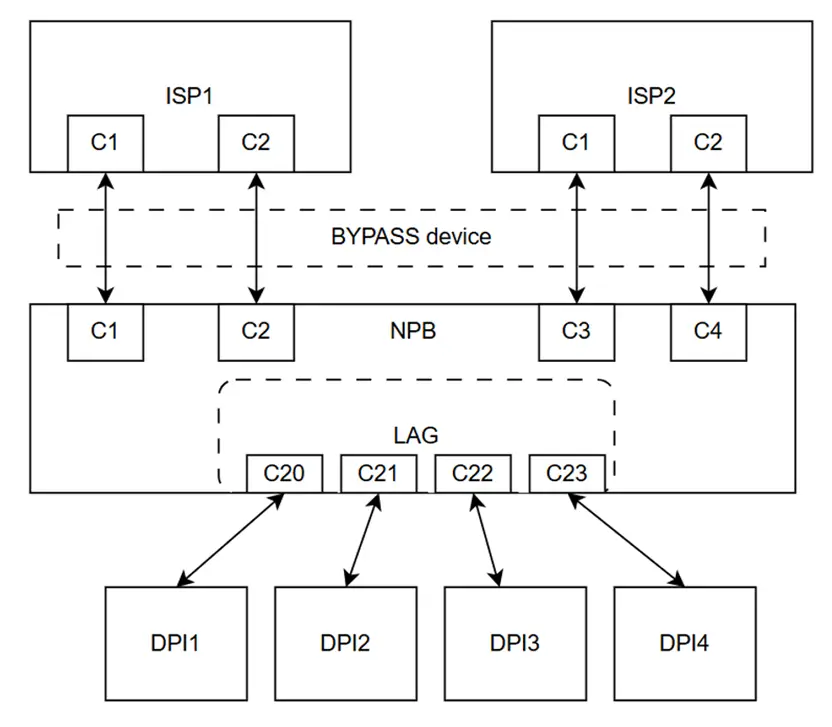
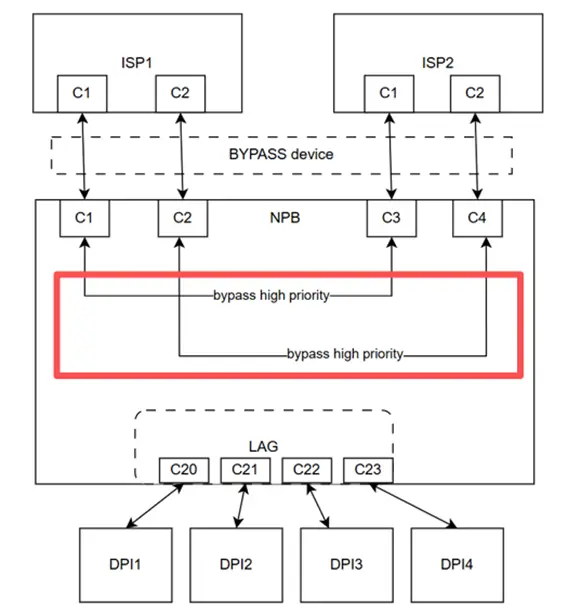
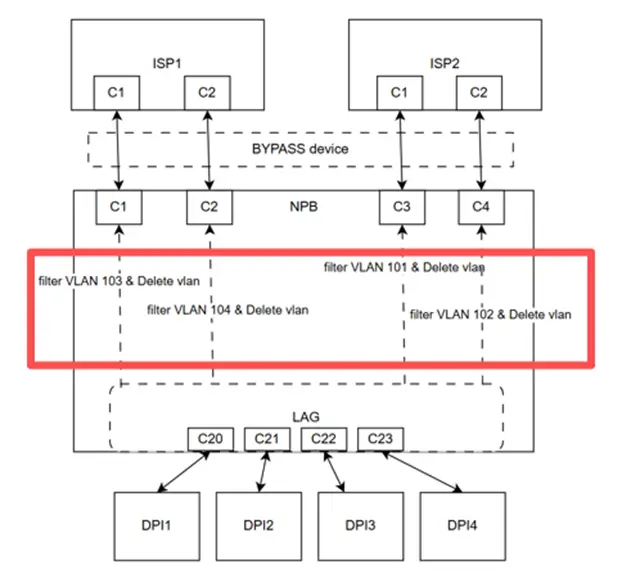
The NPB is deployed inline on the original link, such as between ISP1 and ISP2, with a bypass device added.
If the NPB fails or undergoes an upgrade, the system automatically triggers bypass switching. This ensures that the original traffic continues uninterrupted, providing telecom-grade reliability.
Therefore, the traffic flow is: Source → Bypass → NPB → Backend Tool (e.g., DPI) → NPB → Destination
Key Configuration Points:
- High-Priority Traffic Bypass: Traffic that does not require analysis, such as routing protocol frames, is forwarded directly. This prevents abnormal processing by backend DPI devices.

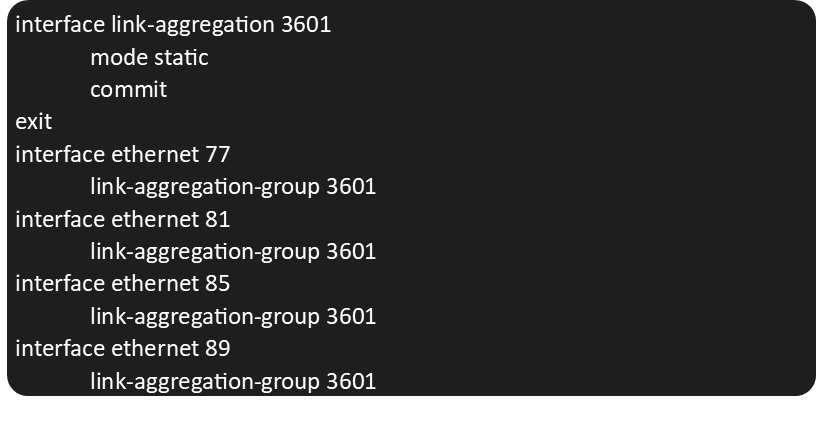
2. LAG (Link Aggregation): Create a LAG group and add the physical ports connected to the DPI device. This ensures load balancing and automatic failover.
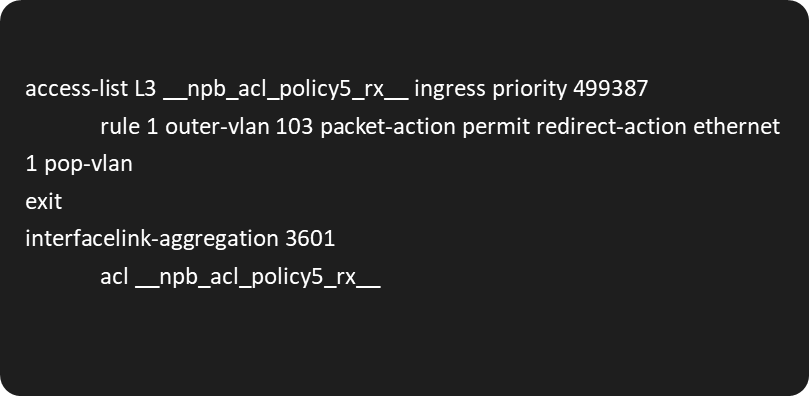
3. Low-Priority Traffic to DPI: Traffic that requires DPI processing is tagged with a dedicated VLAN (e.g., traffic from port C1 tagged with VLAN 101). The VLAN is used for traffic direction identification. After processing, the VLAN tag is removed to avoid impacting the original service.
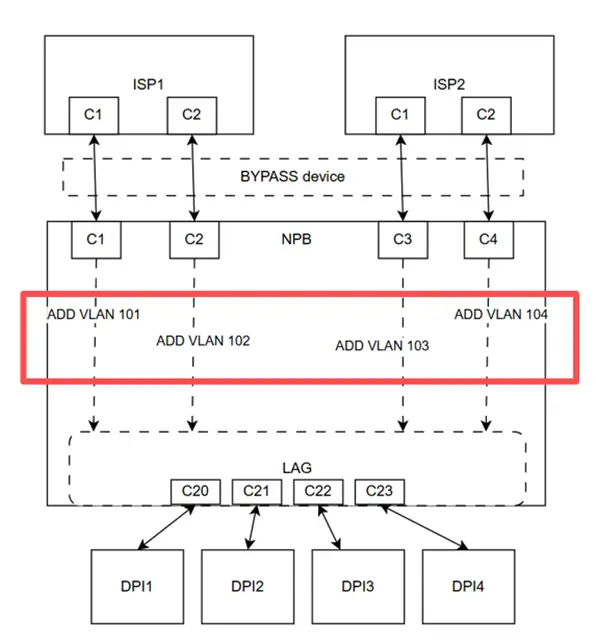
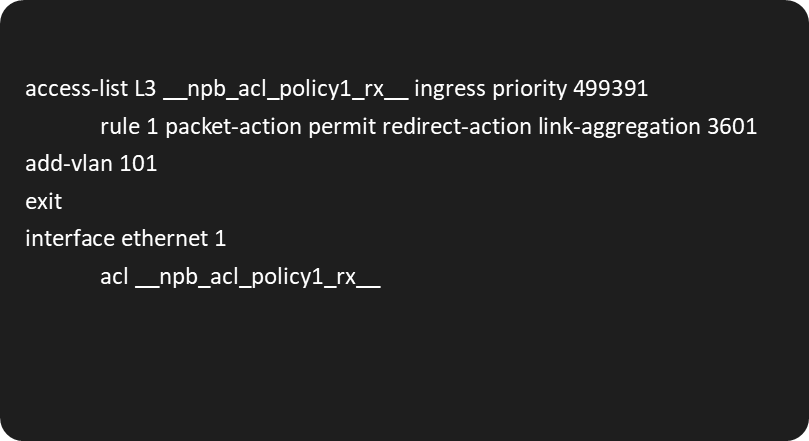
4. DPI Return Traffic Handling: After DPI processing, traffic retains the original VLAN tag when returning to the NPB. Before forwarding to downstream ports, a pop-VLAN operation removes the tag, restoring the original traffic.
Operations and Monitoring
You can use the commands below to check and verify the system’s status and operation:
Quick Reference for Common Commands
| Operation | CLI Command |
| View interface status | show interface status |
| View aggregated interface status | show link-aggregation summary |
| View interface counters | show counters interface |
| Clear interface counters | clear counters interface |
ACL Rule Commands
| Operation | CLI Command |
| View ACL hit statistics | show counters acl |
| Clear ACL hit statistics | clear counters acl |
| View all current configurations | show running-config |
Conclusion
In today’s landscape of complex traffic management and evolving security threats, Inline Packet Broker Deployment stands as a critical solution for the modern enterprise. By moving beyond the limitations of traditional out-of-band monitoring, this approach empowers organizations to achieve active traffic intervention while maintaining peak operational efficiency.
Key Strategic Benefits:
- Optimized Resource Utilization: Precisely filters and distributes only the necessary traffic to backend tools, eliminating resource waste and extending the lifespan of your security stack.
- Enhanced Business Reliability: Integrated high-availability designs and specialized bypass functions ensure zero service interruption, even during maintenance or tool failure.
- Proactive Security Defense: Enables real-time, active traffic manipulation to identify and mitigate threats before they penetrate the core network.
- Reduced Total Cost of Ownership (TCO): Aside from the external bypass hardware, essential reliability features are built directly into the packet broker, significantly lowering long-term capital and operational expenses.
Whether you are looking to harden your infrastructure against sophisticated attacks or streamline your traffic orchestration, Inline Packet Broker Deployment provides the necessary balance of maximum security, high reliability, and cost-effectiveness to safeguard your network’s future.
Have a project in mind? Request a proposal from our sales team at bd@cloudswit.ch
Contact US !
- To request a proposal, send an E-Mail to bd@cloudswit.ch
- To receive timely and relevant information from Asterfusion, sign up at AsterNOS Community Portal
- To submit a case, visit Support Portal
- To find user manuals for a specific command or scenario, access AsterNOS Documentation
- To find a product or product family, visit Asterfusion-cloudswit.ch




